Unlock a world of talent
Hire and manage team members in 240+ countries with compliance and payroll built-in.

Why do customers choose Plane?
Julie Menge
HR Operations Lead, Help Scout

“It used to take hours to deal with monthly payments. The manual process was prone to error because of different banking websites and payment processors. Now, that hours-long operation takes about 10 minutes! Above that, many of our contractors now receive better exchange rates.”
Juan Caviglia
Co-Founder, Meitre

“For a long time, I’ve been looking for a solution to quickly process many payments at once. Finally, someone figured out a simple and powerful tool. Everything we need is here and features are being added each week. On top of all this, the team is super dedicated with magnificent support.”
Caelan Urquhart
CEO and Co-founder, Pipekit

“I’m very happy with Plane, and our contractors are happy as well. I definitely recommend Plane for contractors, especially for global contractor payments. That’s an impressive product.”
Thomas Hollands
Marketing Generalist, Wren

“Plane was enormously helpful for me to be able to take a job that I really enjoy and to be able to work effectively.”
Karl Hughes
Founder, Draft.dev

“I only hear good things from our contractors about Plane — how simple it is and how easy it is to get their money and see when they’ll get paid.”
Kyle Maurer
Director of Operations
“Plane is the solution I've been wishing for a long time! Plane has achieved the impossible: paying our international team is just as easy as paying our domestic one. Also, the Plane team has been incredibly responsive to all of my requests, no matter how small.”
Built for US-based companies hiring anywhere
Hire and pay in the US and 240+ countries.
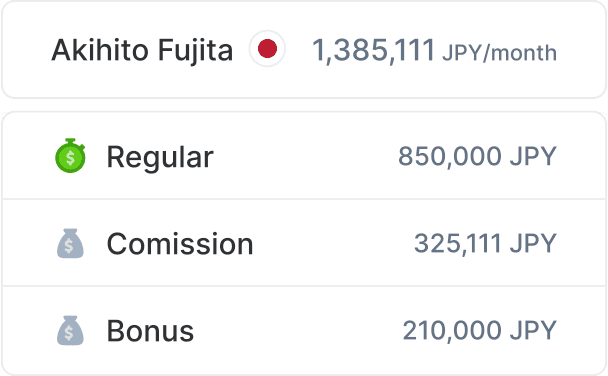
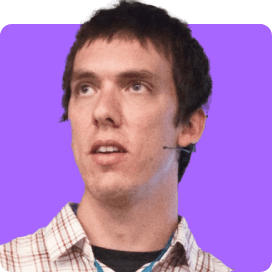
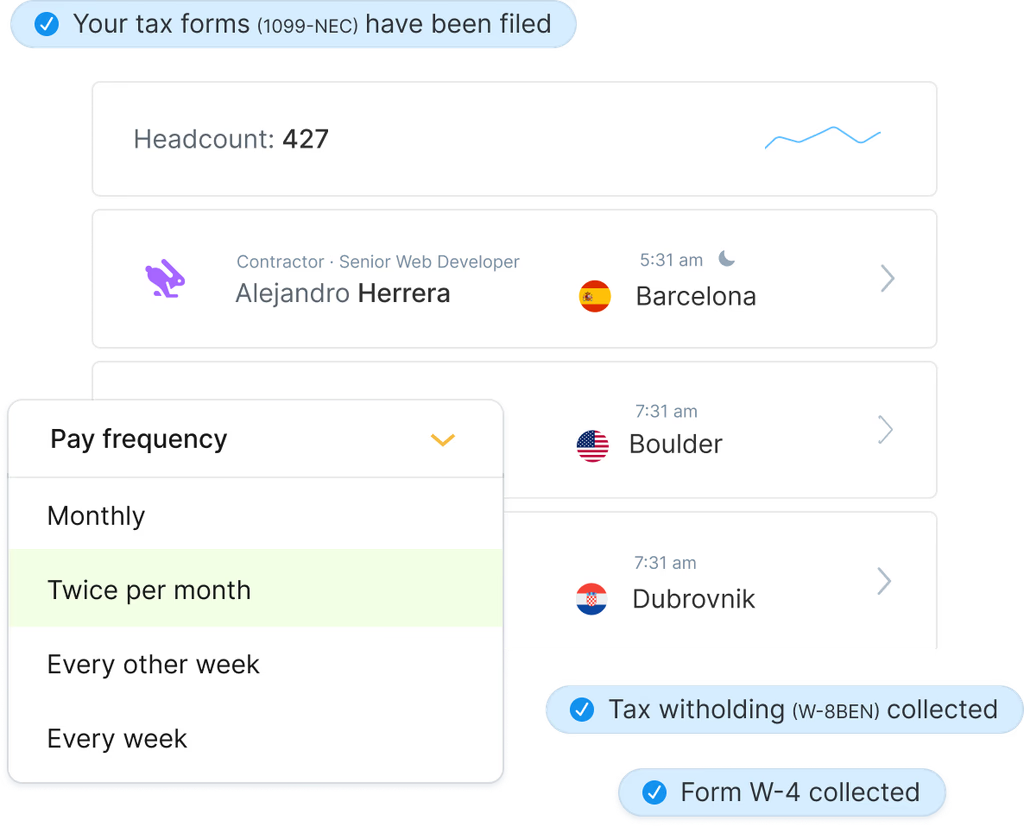
Run payroll for your entire team
Hire and pay employees & contractors in the US and internationally, from one screen. Pay your entire team in just a few clicks.

Get a platform that scales with you
Plane grows with you as your needs change, with automated payments, in-country compliance, and custom workflows from simple to complex
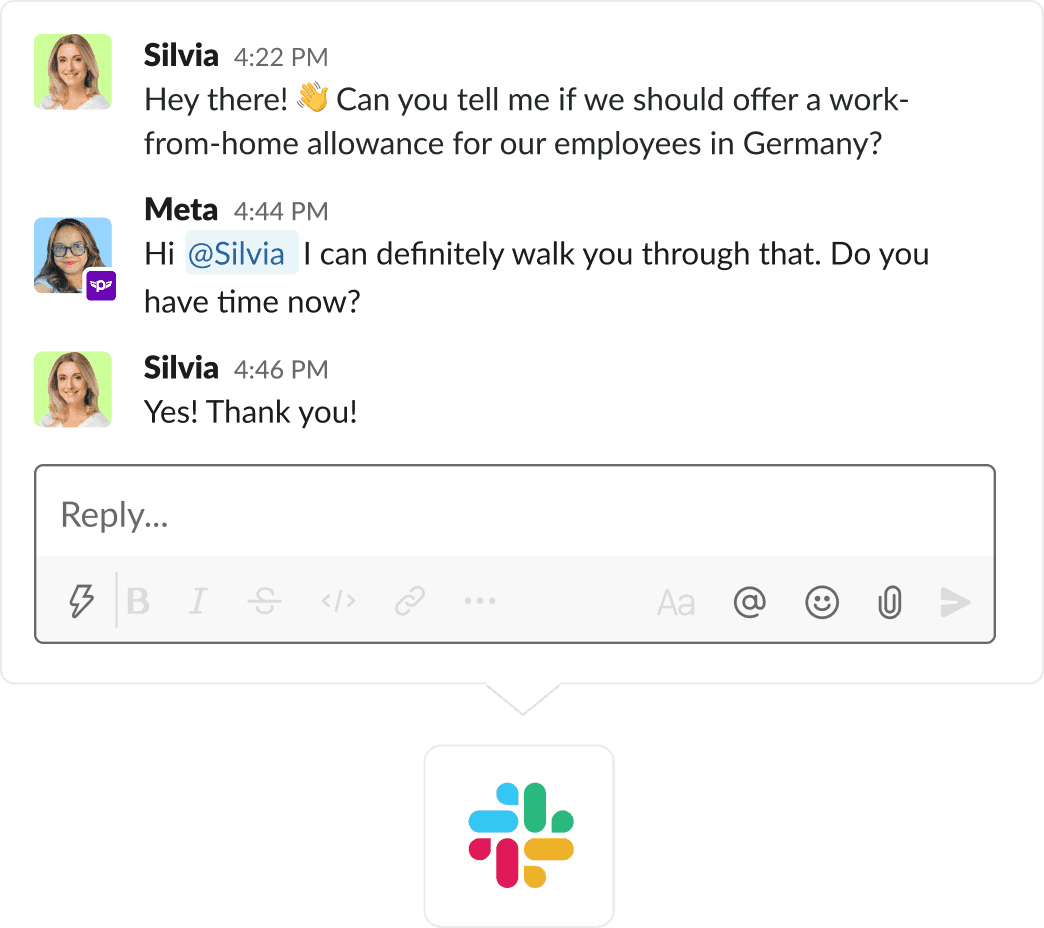
Receive exceptional Slack support
Get your questions answered quickly with our knowledgeable 24/5 support, available via Slack, chat, and email
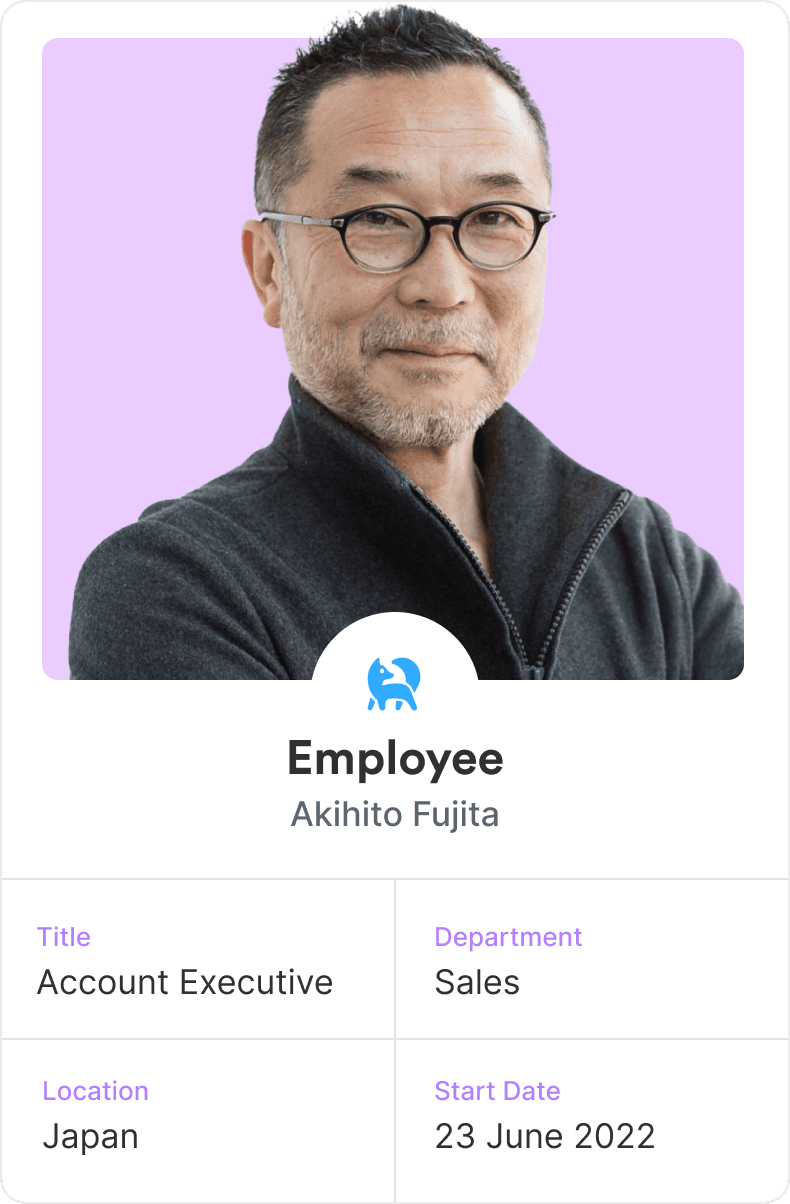
One platform for your entire team
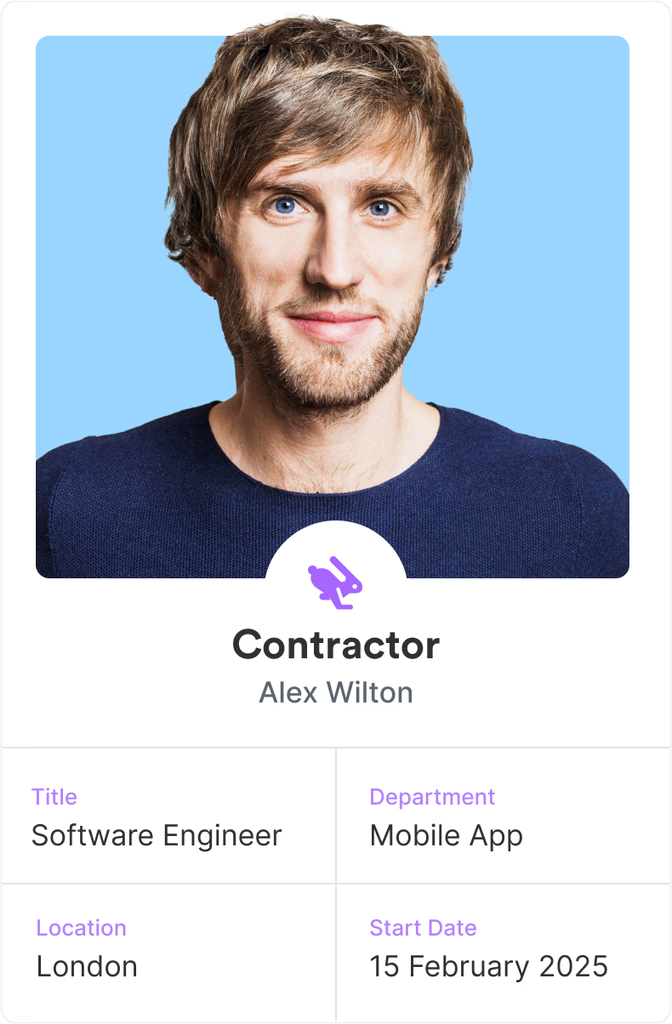
Manage everyone in one place, regardless of their location and contract type.
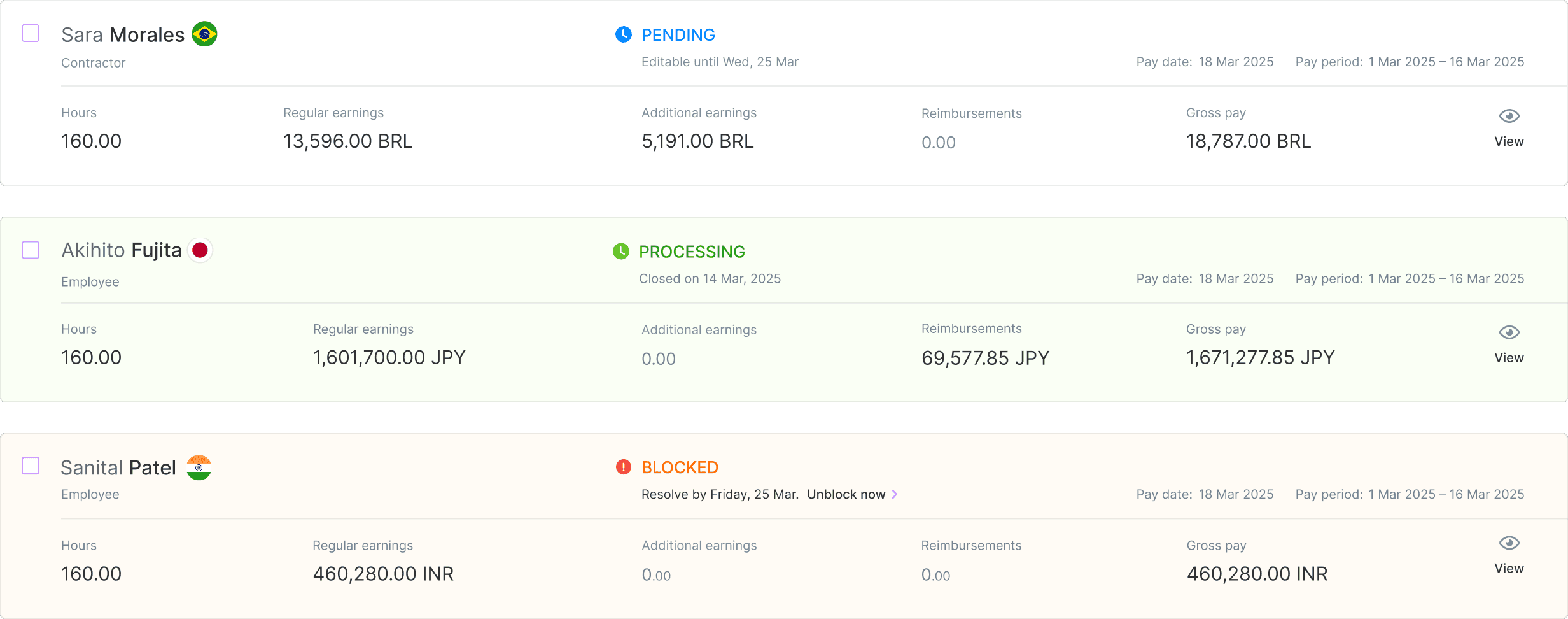
Run payroll for both contractors and employees on one screen
Next
Hire and pay contractors in 240+ countries
Pay contractors in the currency of their choice. Local currency payments and bank transfers are available in 70+ countries.
Use Plane as your EOR in 100+ countries
Hire international employees in days, without setting up local entities, when you use Plane as your employer of record
Run payroll for your US (W2) employees
Hire and onboard US employees using our comprehensive multi-state W2 payroll
HRIS included for everyone
Onboard your whole team in one platform, see PTO for everyone at once, easily pull team data for custom reports, and more
Customer stories
Hear how Plane has made payroll and HR easier for our customers.
How AngelList streamlined contractor payments using Plane
Since partnering with Plane, AngelList has seen significant time savings and no longer pays costly transaction fees.
How Wren used Plane’s EOR services to hire and move a team member internationally
Enlisting Plane to move a team member from being a contractor in Switzerland to an employee in Canada (during a pandemic).
How PadSplit reduced fees and automated payments using Plane
Since switching to Plane, PadSplit has streamlined payments and significantly reduced fees for their contractors.
How AngelList streamlined contractor payments using Plane
Since partnering with Plane, AngelList has seen significant time savings and no longer pays costly transaction fees.
Read the story
Stay in control (and compliant) as you grow
Plane is designed to support companies as they expand.

Grow from 1 to 1,000 employees and contractors
Does your payroll platform have several features you don’t need, but they keep trying to upsell you anyway? Plane offers simple, useful components that you can combine to meet complex needs as you grow.
Set it and forget it, with automated payments
We like automating your manual work for you. Set up automated payments once, and we’ll take care of the rest.
Automated tax compliance
Plane takes care of your compliance needs, including collecting W-8 and W-9 forms, submitting your 1099, and incorporating I-9 completion into onboarding
Local compliance, wherever you’re hiring
Get localized contracts for contractors and employees and expert help on your local compliance questions

Talent knows no borders.
It’s not contained to a 20-mile radius.
We often miss out on the magic of finding the most exceptional people that could propel us forward because we get stuck figuring out the logistics.
At Plane, we believe your focus should be on finding and fostering the best talent the world has to offer, so we built the platform to help you do it.
Not only can you hire and pay your whole global team through Plane, but you can also give everyone a world-class payroll and HR experience, regardless of whether they’re a contractor or employee. We’ve fully supported both worker types from day one, from giving them full access to the platform to direct customer support from our team. Treat your team right with Plane.
— Matt Drozdzynski, CEO at Plane
Learn what contractors are saying about Plane.
Superb support for your whole team
Receive thoughtful support from friendly, knowledgeable humans — not chatbots — on Slack.
Get questions answered quickly for you, your contractors, and employees
No need for you to act as a go-between. Our team is available 24/5 to answer questions directly for you and your entire team.
Expert help for complex questions
Have questions about local employment laws or immigration? Get advice on compliance and immigration from our team of experts.
Friendly, consultative sales team
We don’t believe in hard-selling. Our sales team is happy to offer advice on your HR and payroll needs. If Plane isn’t the best match for you now, we even like to suggest alternatives.

Ready to dive in?
Talk to our team today.
Made with 💜️️️️ all over the 🌎